Cybersecurity

Sciences & Technology
Research
Do you think like an intelligence analyst?
Australians may not be considering a career as intelligence analysts because they’re unsure what skills they need. A new study aims to find out how much we understand about how analysts think, and you can help

Sciences & Technology
The splendour of cybersecurity
Young people may be social media savvy but many need help with the Big Four of cybersecurity. A free device Tune Up gave hundreds a chance to learn

Health & Medicine
Medibank’s hack tells us privacy laws need to change
Medibank’s data breach exposes how Australia’s most vulnerable have the most to lose when private information is made public

Sciences & Technology
Under the Microscope
Using maths to prove computer security
Eureka prize winner Associate Professor Toby Murray thought maths was boring, but he now relies on it to secure critical systems like those of Defence against hackers
Business & Economics
Directors’ duties and cyber security - it’s complicated
Effective management of cyber security risks is a core governance concern but the imposition of a new mandatory directors’ duty would be a step too far

Sciences & Technology
TikTok captures your face
TikTok is hugely popular. But its latest decision to capture unique digital copies of your face and voice is a cybersecurity threat to your identity and privacy
Health & Medicine
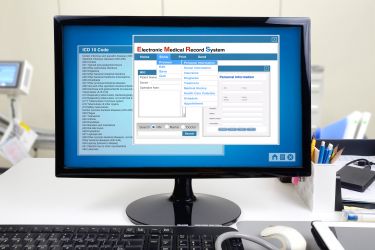
The dark side of electronic medical records
Clinical decision support systems help doctors ‘do the right thing’ by their patients, but they can also be exploited – Australia needs to think about regulation sooner rather than later

Health & Medicine
Regulating medical devices in the ‘Internet of things’
New research explores the gap between regulation and practice in healthcare devices, particularly for type 1 diabetes, that are part of the Internet of Things

Sciences & Technology
Are you technostressed?
As many of us continue to work from home during COVID-19, there’s increasing incidence of technostress and techno-overload among workers that needs to be addressed

Politics & Society
Do we really need a tracking app and can we trust it?
Privacy and transparency should be central to the use of a COVID-19 tracking app, but there are other ways to track infections, and an app may not work anyway