
Sciences & Technology
Paper audits crucial for automated counting

Voters casting their ballot online must be able to trust the process. In a world where hackers have been accused of interfering in elections, iVote is not the answer
Published 5 March 2017
In the 2017 Western Australian state election, voters with disabilities can register and vote over the Internet for the first time, using a system called iVote. Voters with disabilities deserve to have just as much confidence in the privacy and security of their votes as able-bodied voters using a polling booth. Unfortunately, a breach of voter privacy, or overt tampering of ballots, may not be noticed if it happens online – and reading or altering someone’s iVote might be easier than it seems.
Security vulnerabilities are successfully exploited every day to steal money, commit financial fraud and extract government secrets. US intelligence agencies blamed Russian government hackers for interfering in the US election.
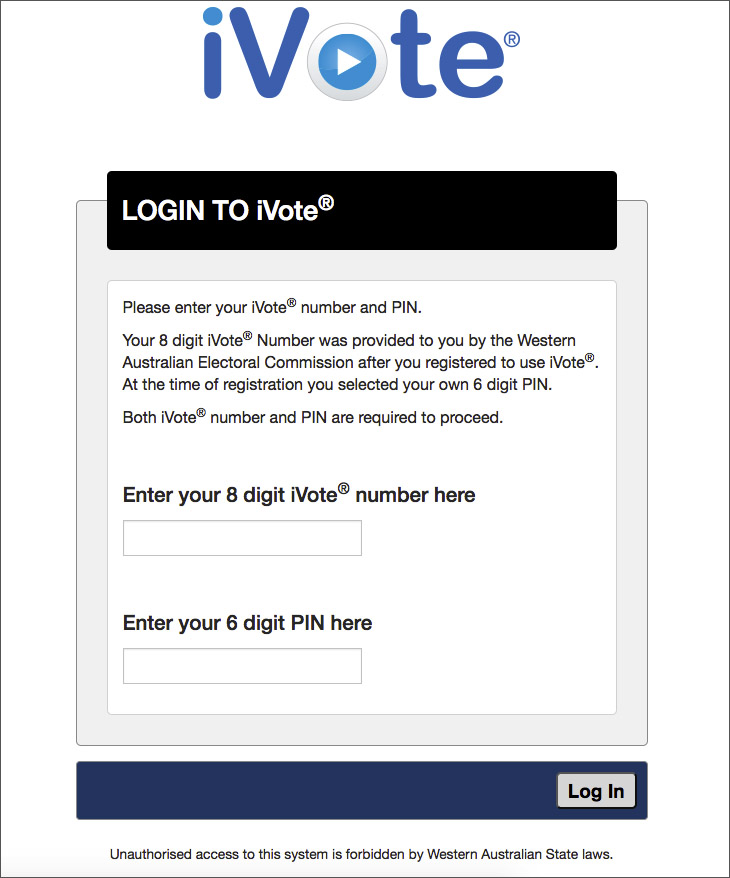
The iVote registration and voting servers are protected by Transport Layer Security (TLS), the Internet’s most common security protocol. If you visit your bank and click on the padlock in your browser’s address bar, you can see a TLS certificate that proves you are communicating with the true owner of that domain. However, if you visit the WA Electoral Commission’s online registration page or the iVote log-in page and click on that padlock, you see something surprising: the TLS certificate is owned not by the WA Electoral Commission (WAEC) but by a US company called Incapsula.
Incapsula provides protection against Distributed Denial of Service (DDoS) attacks, by placing itself between voters and the actual iVoteserver. This is known as a ‘proxy’.
It means that registration information of WA voters is sent to an Incapsula server based in the US (107.154.128.220), where it is decrypted, allowing anyone with control of Incapsula’s servers to read it. (We are not eligible to register, so we don’t know whether Medicare and passport numbers of voters are also sent there.)
This is not a question of Incapsula being dishonest: possible eavesdroppers include Incapsula employees, contractors, hackers who may have compromised Incapsula’s systems, and the US Government itself. Incapsula’s competitor, Cloudflare, was recently affected by a serious security problem which leaked passwords, secret keys, intimate photos and other private data.
iVote aims to provide a secret ballot by separating the registration server (which knows your identity) from the voting server (which can learn how you voted). Unfortunately, the use of Incapsula to proxy voter connections destroys this separation. If you register and vote from the same web browser, a ‘cookie’ stored on your system by Incapsula allows it to link both interactions.
iVote ballots are encrypted using code provided by the voting server (ivote-cvs.elections.wa.gov.au). Our tests showed that this voting server is physically located in Sydney, not WA. The encryption is only as trustworthy as the server providing the code. Anyone with access to Incapsula’s systems, or the NSW server, could manipulate this encryption code before it reaches the voter, allowing them to read or modify votes before they are returned to the voting server.

Sciences & Technology
Paper audits crucial for automated counting
Indeed, actively modifying the code may not be necessary for a server that knows registration information. iVote stores partial votes on the voting server – knowing a voter’s PIN might make it significantly easier to guess their ID number and hence decrypt their vote. Since we are not eligible to use iVote, we have not been able to confirm whether this is feasible.
This is a question of trust. The WA Electoral Commission (WAEC) has assured voters that their votes are “completely secret” and “cannot be tampered with or changed”. Unfortunately, the commission cannot ensure that either of these statements is true, especially if the connections are proxied through a third party.
Despite its marketing claims, iVote is not a verifiable voting system. The telephone-based vote-reading service does not give voters any genuine evidence that their votes are properly recorded and included in the count, nor does iVote give scrutineers any meaningful opportunity to verify that votes have been properly processed.
The last time iVote was used for a state election (NSW 2015), there was at least one serious security vulnerability. There is no evidence that it was exploited to manipulate votes — but also no evidence that it was not. This is the key problem with the use of online voting systems such as iVote: the verification protocol does not guarantee that errors or fraud will be detected.

Sciences & Technology
Crime and privacy in open data
After the 2015 election, the NSW Electoral Commission claimed that “1.7% of electors who voted using iVote also used the verification service and none of them identified any anomalies with their vote”. However, more than a year after the election, it emerged that 627 calls to the verification service failed to retrieve any vote at all – a failure rate of approximately 10%. We don’t know whether these errors were caused by voter error, software bugs or deliberate manipulation. All we know is that the system isn’t verifiable, because an indication of a serious problem does not seem to have been noticed or mentioned to scrutineers at the time.
Secure, private and verifiable online voting remains an unsolved problem. Online voting involves a unique challenge to keep votes anonymous while producing evidence of a correct outcome — which is not found in other systems such as online banking.
There is no suggestion that any of the parties described in this article would act maliciously. However, when dealing with security, it is the risk that matters. Using a proxy such as Incapsula simply adds to a list of parties who may have the ability to read or modify iVote ballots without being detected. The software vendor (Scytl), or attackers with access to their systems, could add malicious code to the iVote system which would be very hard to detect. Those with (legitimate or illegitimate) access to WAEC servers or the NSW host server might also be able to modify the code, as could anyone who controlled the voter’s computer.

Sciences & Technology
Understanding the maths is crucial for protecting privacy
The WA Electoral Commission has built up well-deserved trust among WA voters and candidates over many years, but this trust does not automatically transfer to others. Scrutineers have no meaningful way of verifying iVote’s output. Scrutineers based in WA will not even be able to see the iVote server in Sydney that receives WA votes from the United States.
Paper-based voting, crucially, is beyond the reach of a remote cyber attacker such as a foreign government. We strongly recommend that the WA Electoral Commission discontinue the use of iVote for future WA state elections, and reintroduce VoteAssist, a polling-place system that allowed voters to verify a printed paper record of their vote.
Secure e-voting can work in the privacy of the polling booth, using a paper record so that voters can verify their vote matches their intention. Voters with disabilities shouldn’t have to trust another person, but they shouldn’t have to trust a computer either. On the Internet, you might not even know who is voting for you.
Disclosure history: On February 17 we sent a letter to the WAEC explaining these concerns. Separately, we followed up with specific advice that the core iVote server was not adequately protected from DDoS attacks. This meant that anyone who could find the internet address of the voting server could potentially DDoS it directly, bypassing Incapsula entirely. The specific DDoS advice appears to have been followed, so the server is now much better defended. The trust issues described in this article remain.
Authors’ note: Since publication, the WAEC has pointed out that connections within Australia are generally sent to Incapsula servers in Australia, not California. However, our research shows there are numerous Incapsula servers throughout the world serving valid certificates for *.elections.wa.gov.au, including servers in the USA, UK and China, and any one can be used as a proxy. If one was compromised, the secret key could be used to impersonate *.elections.wa.gov.au anywhere in the world, including within Australia.
Banner image: Shutterstock